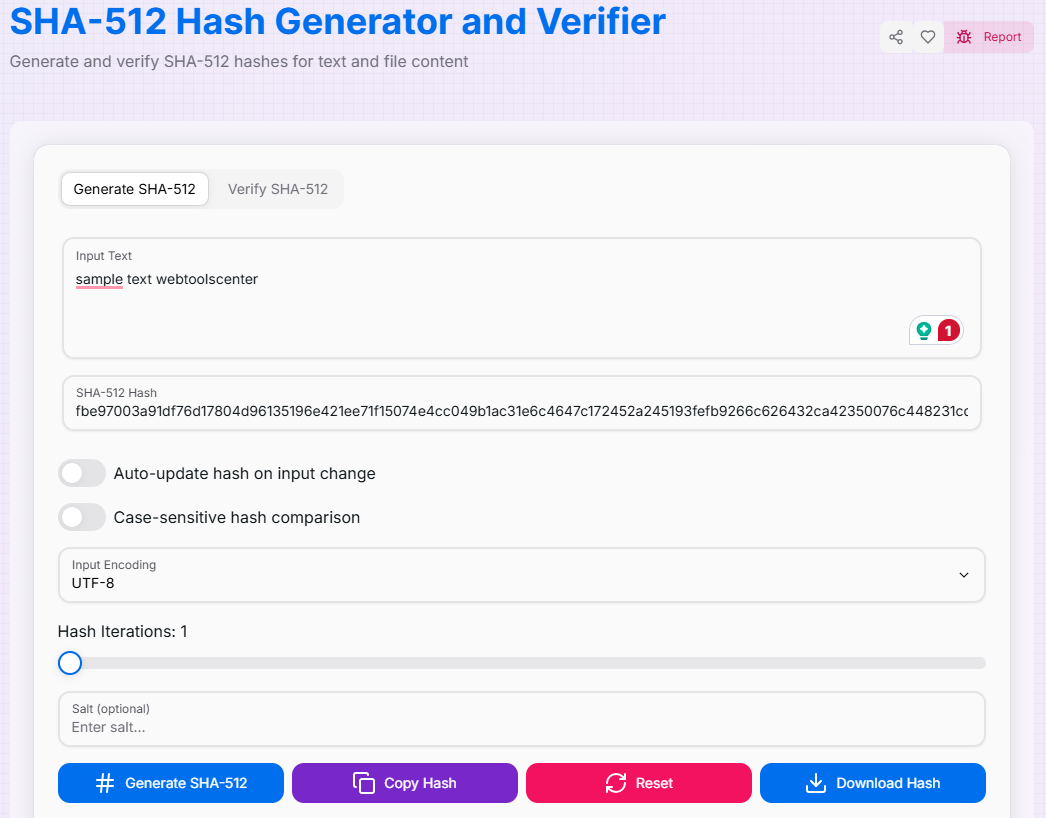
SHA-512 Hash Generator and Verifier
Generate and verify SHA-512 hashes for text and file content
Hash Iterations: 1
What is the SHA-512 Hash Generator & Verifier?
Think of the SHA-512 Hash Generator & Verifier as the heavyweight champion of data integrity. As the most robust member of the SHA-2 family, it produces a massive 512-bit (64-byte) cryptographic digest. This extremely long hash value provides an unparalleled level of security, making it virtually immune to collision attacks with current computing power.
Whether you are an enterprise developer ensuring the authenticity of mission-critical data, a security engineer creating digital signatures for government-grade systems, or a privacy enthusiast hardening passwords, this tool provides the highest standard of protection. It allows you to generate hashes from text or files, implement custom salting, and perform real-time verification to ensure your data remains untampered and secure.
How to Use the SHA-512 Hash Generator & Verifier?
- 1Input Your Source:
Enter your text directly in the input field or upload a file to generate a checksum. Choose your encoding method (UTF-8, ASCII, or Base64) for accurate data interpretation.
- 2Enhance the Hash:Salts & Iterations:Add a custom salt value to defend against rainbow tables and configure the number of iterations to increase the computational difficulty for brute-force attacks.
- 3Generate & Compare:
The SHA-512 hash is generated in real-time. To verify authenticity, navigate to the Verification tab and paste an existing hash to see if it matches your input.
- 4Save & Export:
Save your favorite configurations as Presets (). Copy () the resulting hash or Download it as a file.
Key Features of SHA-512
Security Considerations & Tips
Passwords
While SHA-512 is extremely secure, for password storage, it is best used with key-stretching algorithms like Argon2, bcrypt, or PBKDF2.
One-Way Function
Hashing is permanent. Original data cannot be "decrypted" from a hash; it can only be verified by generating a new hash from the same input.
CPU Intensive
SHA-512 is more computationally demanding than SHA-256. Use it in environments where security is the absolute priority over raw throughput.
Applications and Use Cases
Meeting high-compliance standards for sensitive document authentication and high-stakes data integrity.
Generating unique signatures for software binaries and certificates to prove origin and prevent unauthorized modifications.
Creating virtually unique keys for large database records and files to manage assets without collisions.
Ensuring that audit trails and digital records are tamper-proof for security logging and legal requirements.
The SHA-512 Hash Generator & Verifier is the ultimate tool for anyone requiring top-tier cryptographic security. By combining the industry's most robust algorithm with advanced features like iterative salting and real-time verification, you can safeguard your data with the highest confidence. Secure your digital legacy today!