SHA-1 Hash Generator & Verifier
Generate and verify SHA-1 hashes with advanced options and features.
What is the SHA-1 Hash Generator & Verifier?
Think of the SHA-1 Hash Generator & Verifier as a sophisticated digital seal for your data. In the landscape of data integrity, SHA-1 (Secure Hash Algorithm 1) takes an input of any size and produces a unique 160-bit (20-byte) "message digest." This fixed-size string acts as a unique identifier for the original content.
While SHA-1 has been deprecated for high-security cryptographic tasks due to theoretical vulnerabilities, it remains an industry standard for non-cryptographic integrity checks. It is widely used in version control systems like Git, data deduplication, and legacy system maintenance where verifying that a file remains unchanged during transmission is the top priority.
How to Use the SHA-1 Hash Generator & Verifier?
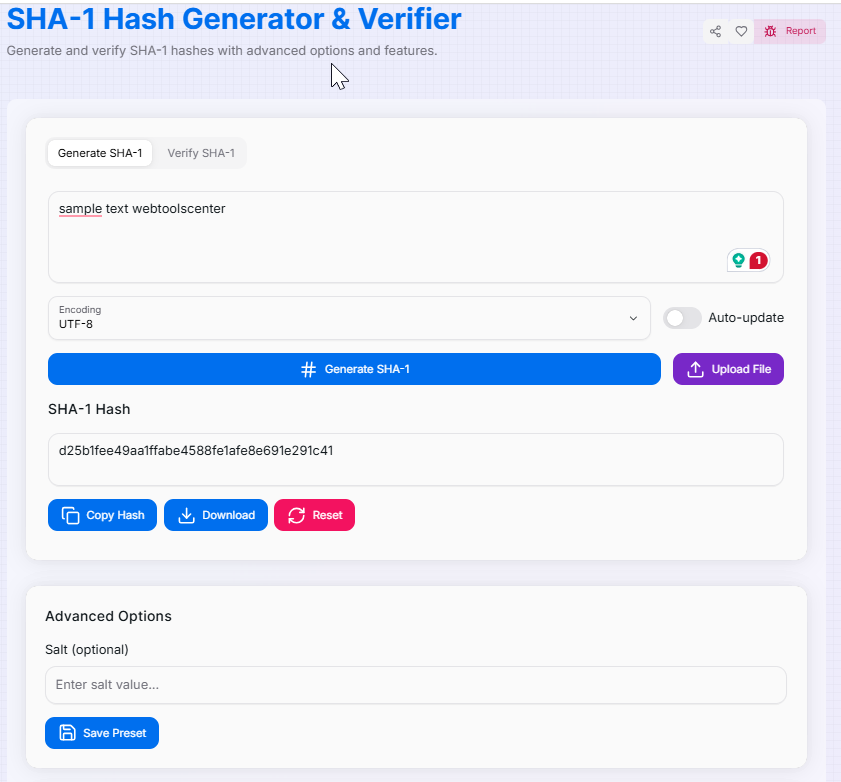
- 1Provide Input:
Enter your text in the input area or use the File Upload feature to process local documents. Choose your encoding: UTF-8, Base64, or Hex.
- 2Configure Security:Salting & Presets:Optionally add a salt value to strengthen the hash. You can also save your configuration as a Preset () for recurring tasks.
- 3Generate or Verify:
The tool generates hashes in real-time. To confirm integrity, switch to the Verify tab, paste an existing hash, and toggle between case-sensitive or insensitive comparison.
- 4Export Result:
Copy () the hash to your clipboard or Download the result as a text file. Use Reset () to clear all fields.
Key Features
Security Considerations
Cryptographic Deprecation
SHA-1 is considered cryptographically broken for security-critical tasks. It is vulnerable to collision attacks and should not be used for password hashing or SSL certificates.
Recommended Standards
For security-sensitive applications, always use stronger algorithms like SHA-256 or SHA-3. Use HTTPS to protect hash transmission.
Applications and Use Cases
Data Integrity
Quickly verify that files or code snippets haven't been tampered with or corrupted during transfer.
Version Control
Understand the underlying mechanics of Git and other systems that use SHA-1 for file identification.
Legacy Systems
Generate hashes for older infrastructures that still require SHA-1 while planning for future migration.
The SHA-1 Hash Generator & Verifier is a valuable tool for understanding the foundations of data hashing. While it's vital to recognize its limitations in modern security, it remains a powerful ally for everyday data verification and educational insights. Master your data integrity today!